Twelve years ago, the mysterious Satoshi Nakamoto introduced a game-changing innovation to the world when he published the revolutionary Bitcoin whitepaper titled “Bitcoin: A Peer-to-Peer Electronic Cash System.” This 9-page document paves the way for remarkable developments in various industries today.
This document may not be the easiest thing to read. So, to mark its 12 years of existence in the world, let us walk you through different sections of the Bitcoin Whitepaper while making sure you understand every part of it without breaking a sweat!
Bitcoin White Paper Quick Facts
On October 31, 2008, this revolutionary white paper was published by Nakamoto on the metzdowd.com cryptography mailing list. The paper has 12 parts, which we’ll look into in a bit. In the email, he mentioned that the electronic cash system—Bitcoin (BTC)—is fully peer-to-peer (P2P), “with no trusted third-party.”
What do all of these mean exactly? Let’s take a look at the first part of Bitcoin’s white paper.
Abstract
The first line of Bitcoin’s white paper reads:
“A purely peer-to-peer version of electronic cash would allow online payments to be sent directly from one party to another without going through a financial institution.”
As a digital currency, Bitcoin aims to make direct payments possible. This eliminates the need for any third-party services like banks and other financial institutions to complete any monetary transaction.
“Digital signatures provide part of the solution, but the main benefits are lost if a trusted third party is still required to prevent double-spending. We propose a solution to the double-spending problem using a peer-to-peer network.”
On the flip side, one of the most common problems digital currencies face is double-spending. Bitcoin solves this problem through its robust network and very complex systems that are nearly impossible to compromise.
How is that even possible? Let’s find out.
1.Introduction
When you shop online, you often use a credit or debit card, mobile payment applications, or other cashless electronic systems to pay. These payment options are considered third-party solutions and are under a trust-based model. While payments are seamlessly processed most of the time, third-party service providers are still susceptible to various risks like fraud, lack of robust security features, and other possible platform or system interferences.
That’s the main problem that Nakamoto addresses through Bitcoin. This unique form of money uses a peer-to-peer network to facilitate direct payments and eliminate different transaction issues like the reversibility of payments in online transactions. You might ask, “Is the reversibility of payments really bad?” Well, in online transactions, there are a lot of potential risks that come along with it.
When you buy goods and services online, you face the possibility of a failed delivery, receiving wrong or damaged items, and more. On the other hand, when you sell stuff online, you face the risk of not getting paid, dissatisfaction with the items or services you sold, and more.
Transaction disputes like these aren’t an easy fix. Each scenario has a different outcome that will depend on payment reversibility, especially when it’s done through a third-party. The resolution process won’t only take a lot of time, but also potential costs for item or payment refunds—an upsetting event for both the buyer and seller.

With Bitcoin, transactions are irreversible. This paves the way for reduced transaction risks that often come with traditional payment systems and third-party solutions. Instead of trust, Bitcoin uses cryptographic proof, so both parties can transact directly with one another. However, digital currencies are susceptible to double-spending or the possibility of spending the same money more than once.
Bitcoin prevents this from happening through its very complex systems and processes that are computationally impossible to reverse. It uses routine escrow mechanisms, P2P distributed timestamp servers, nodes, and other powerful technologies to provide a whole new level of payment processing of digital transactions.
2. Transactions
To eliminate the use of third-party services and prevent double-spending, Nakamoto created an electronic coin defined in the White Paper as a chain of digital signatures. These signatures serve as records of BTC’s whereabouts.
Before a coin is transferred, the current owner must digitally sign the previous owner’s hash—a unique Bitcoin transaction identifier—and the next owner’s public key as a record of ownership history.
Picture this scenario: You received a check with a value of $1,000 in an envelope with the previous owners’ signatures and addresses written on it. To send that check to someone else, you also need to put your signature and address on the envelope and write the address where you’ll send it to.
In the Bitcoin Whitepaper, BTC transactions look like this:
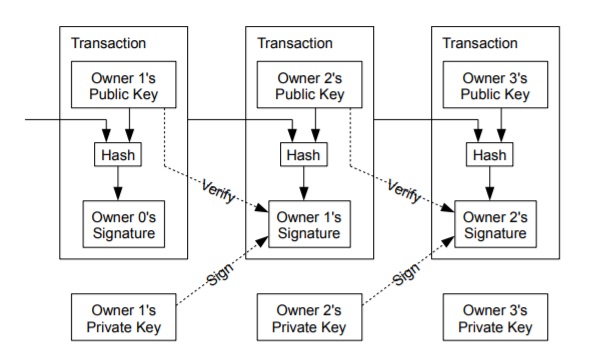
Now, let’s say you didn’t have any problems with sending the check to someone else. But how can you be sure that the check is legit and that no one had cashed out and spent it yet before you received it? You can probably look into the list of every check cashed out in the country, but that will only be possible if the public can view the checks’ serial numbers.
That’s how Nakamoto designed Bitcoin: transparent and accessible to everyone in the network. Each user in the Bitcoin network can see where each BTC came from and where it’ll go. But how?
Let’s move on to our next point.
3. Timestamp Server
“The solution we propose begins with a timestamp server. A timestamp server works by taking a hash of a block of items to be timestamped and widely publishing the hash, such as in a newspaper or Usenet post.”
Simply put, the timestamp server guarantees that a transaction happened at some point in time. Timestamps are often referred to as “proofs-of-existence” since they can confirm whether or not data existed previously.
4. Proof-of-Work
Proof-of-Work (PoW) is a consensus algorithm that validates transactions on the Bitcoin network. To verify a transaction, it needs to be confirmed by the network. Now, these data aren’t confirmed and validated one by one. Each transaction is grouped into blocks, which are not only difficult to confirm, but also to create.
When Bitcoin transactions are confirmed and broadcasted on the network, they become impossible to reverse due to their complex nature. If someone attempts to reverse a BTC transaction or double-spend a Bitcoin, they will have to revisit all the transactions made in the confirmed blocks that come after their transaction and reverse all of them—now that’s a really tough job!
5. Network
According to Nakamoto, these are the steps to run the Bitcoin network:
- New transactions are broadcasted to all nodes.
- Each node collects new transactions into a block.
- Each node works on finding a difficult Proof-of-Work (PoW) for its block.
- When a node finds a PoW, it broadcasts the block to all nodes.
- Nodes accept the block only if all transactions in it are valid and not already spent.
- Nodes express their acceptance of the block by working on creating the next block in the chain, using the hash of the accepted block as the previous hash.
You probably noticed that every item has the word “node” in it. So what is a node? A node is referred to as a computer that runs the Bitcoin program. This computer is connected to other computers that have the same program and create a Network.
To help you understand a node’s role on the network, here are its three critical functions:
- Follow a set of instructions – For example, a node was programmed to receive transactions worth 3 BTC and above. If the node receives a transaction below that amount, then it won’t relay that transaction.
- Share information to other nodes – The two main types of transactions that nodes share are fresh—single transactions that have recently entered the network; and confirmed—those that have been confirmed and are shared in blocks.
- Keep a copy of confirmed BTC transactions – Nodes keep a block of confirmed transactions. On the other hand, fresh transactions “bounced around the network,” grouped into blocks, confirmed by miners, and then added in sequential order—hence the blockchain, the ledger of confirmed blocks. Adding a fresh transaction to the blockchain is called mining—the tedious process of acquiring BTC.
Simply put, nodes are “miners” who group the transactions entering the network and add them to the blockchain.
6. Incentive
Mining Bitcoin isn’t an easy job. Miners use not only their impressive technical knowledge to solve highly complex mathematical problems, but also a lot of other expensive resources. These include high-powered computers and mining equipment, a stable Internet connection, high electricity levels, and specialized mining software.
But why are these miners willing to spend their money, time, and energy on this tedious process? Is Bitcoin mining profitable? Of course, Bitcoin mining comes with an incentive or reward. The first reward is newly-minted Bitcoin and the second is transaction fees. The amount of the reward varies depending on the difficulty level of mining the BTC. Also, there’s this thing called “Bitcoin Halving,” but that’s another story for another time.
The Bitcoin Whitepaper reads:
“The incentive may help encourage nodes to stay honest. If a greedy attacker is able to assemble more CPU power than all the honest nodes, he would have to choose between using it to defraud people by stealing back his payments or using it to generate new coins.”
The rewards waiting at the end of all the extensive mining works keep miners motivated to finish what they started without cheating or tricking the network.
7. Reclaiming Disk Space
“Once the latest transaction in a coin is buried under enough blocks, the spent transactions before it can be discarded to save disk space.”
The transactions being processed in the Bitcoin network are never-ending. That means a lot of data is also stored in the system. However, Nakamoto mentioned in the Bitcoin White Paper that completed transactions don’t necessarily have to be kept and stored in the block.

Before transactions are discarded, their Merkle Roots are collected in the block’s hash. Merkel Root is referred to as “a fingerprint for all transactions in a block.” It is created by hashing pairs of transaction IDs (TXID), which generates a short and unique identification for all transactions in a block. With this, you can check out if a transaction exists in a block without knowing every TXID in there.
8. Simplified Payment Verification
According to Nakamoto, verifying payments on the network is possible even without running a full network node. This can only happen if a user can keep a copy of the longest PoW chain and check if the network has accepted it by linking it to a place in the chain. In the Bitcoin White Paper, the longest PoW chain looks like this:
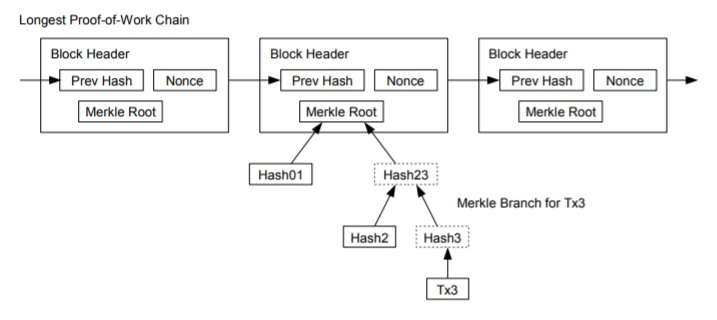
A user can trust the verification as long as honest or reliable nodes control the network. However, there’s a possibility of having fraudulent transactions on the network if an attacker overpowers it. To prevent such attacks, the network nodes send alerts whenever they detect an invalid block. To confirm the network’s inconsistency, the alerts sent by nodes will then prompt the user’s software to download the entire block and alerted transactions—isn’t that interesting?
9. Combining and Splitting Value
This part is quite tricky. Bitcoin’s White Paper reads:
“Although it would be possible to handle coins individually, it would be unwieldy to make a separate transaction for every cent in a transfer. To allow value to be split and combined, transactions contain multiple inputs and outputs. Normally there will be either a single input from a larger previous transaction or multiple inputs combining smaller amounts, and at most two outputs: one for the payment, and one returning the change, if any, back to the sender.”
It’s like you’re buying a cup of coffee worth $4 and you paid $10. With cash payments, you’ll receive an exact amount of $6 as your change. However, with BTC transactions, your change can be many irregular values like $1.53, $0.47, $36.50, and the like.

To use these amounts of BTC to buy something, you’ll have to combine them all. And when you use it, your BTC wallet will have another unusual sum or amount of money as change.
10. Privacy
With traditional banks and other financial institutions, a user’s privacy is maintained by limiting a user’s information to a trusted third party and other possible parties involved. On the other hand, Bitcoin’s privacy model involves announcing all the transactions in the public ledger or the blockchain.
In the Bitcoin White Paper, it looks like this:
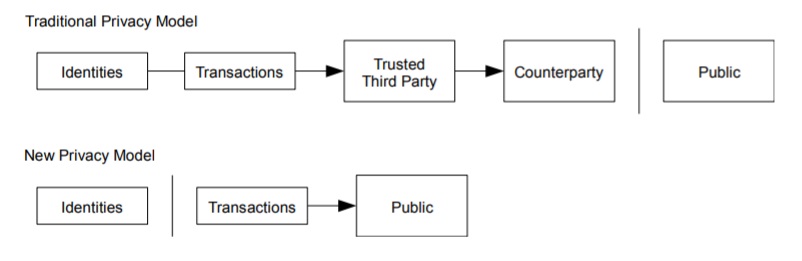
But how can a user’s privacy be maintained in this kind of model? The answer: by keeping the public keys anonymous. On Bitcoin’s blockchain, all transactions are broadcasted and everyone on the network can see that a user is sending Bitcoin to another user. The coolest part is that no one really knows who these parties are, since no personal information links the transaction to anyone.
However, Nakamoto mentioned a potential risk:
“The risk is that if the owner of a key is revealed, linking could reveal other transactions that belonged to the same owner.”
This line confirms that Bitcoin isn’t completely anonymous but pseudonymous, contrary to the common Bitcoin myth.
11. Calculations
Now, this portion of the paper contains a lot of math—like, a lot. But don’t worry, we won’t dip our toes into the pool of mind-bending calculations and algorithms. In this part, Nakamoto explains that it’s highly unlikely for an attacker to “create an alternate chain faster than the honest chain.”
From what we’ve learned in the previous sections of the White Paper, nodes won’t relay information to other nodes once they receive an invalid transaction, and “honest nodes will never accept a block containing them.” This is what makes Bitcoin’s network robust and independent.
We also learned that reversing a BTC transaction is computationally impossible. If an attacker tries to compromise the system and attempts to take BTC funds from other users, they must go back to the previously confirmed transactions and reverse all of them.
Simply put: the attacker’s probability to successfully compromise the network drops exponentially as the number of blocks he has to catch up with increases.
12. Conclusion
We’re now in the Bitcoin White Paper’s final section! So to sum up all the technical knowledge we’ve gathered from sections one to 12, here are some of Bitcoin’s leading properties, according to Satoshi Nakamoto:
- Double-spending is prevented with a P2P network.
- There’s no need for other trusted parties.
- Participants can be anonymous.
- New coins are made from Hashcash style Proof-of-Work (PoW).
- The PoW for new coin generation also powers the network to prevent double-spending.
From all the fascinating technologies, robust systems, and other wonders we’ve learned from this paper, we can probably agree with Nakamoto when he said: “The [Bitcoin] network is robust in its unstructured simplicity.”
Look who made it this far!
Congratulations to you not only for making it at the end of our Bitcoin White Paper discussion, but most importantly, for seeking out knowledge about Bitcoin, blockchain, and other developing technologies in the crypto sphere. There’s more information waiting for you in the actual White Paper, but we do hope this information helps you quench your thirst for crypto knowledge!
If you’re interested to learn more about Bitcoin and how it works, you can always check out our other crypto tutorials. And if you’re ready to try your hand at BTC trading, create your Paxful account now and see how Bitcoin can actually help you.
Good luck on your crypto journey!